Fixing CredSSP encryption oracle remediation in RDP
CredSSP (Credential Security Support Provider) protocol is the protocol which ensures that your credentials for a target server are sent securely...
What’s the whole story about CredSSP?
CredSSP (Credential Security Support Provider) protocol is the protocol which ensures that your credentials for a target server are sent securely when using RDP. Researchers found a security vulnerability late last year that allows for a malicious user to gain access to the server and execute code on the server remotely over the network. This is done with a man-in-the-middle attack where the malicious user is connected to the same network. If you want to learn more about this security vulnerability, watch the video released by the researchers:
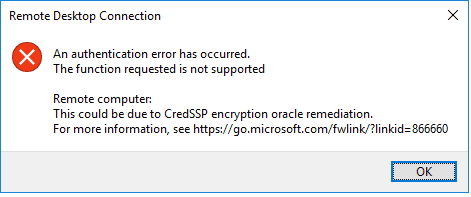
Microsoft released a patch to fix this vulnerability in May 2018. This is available as a Windows Update for many different versions of Windows, including Server versions. Unfortunately, the update can’t be applied to all machines immediately because many servers can’t just be shut down at sudden notice. Due to some machines having the update and others not, the below error appears:
So how do I fix it?
A temporary fix can be employed that will allow you to connect to servers even if they haven’t been updated yet. This is temporary though because I would encourage you to schedule an update for the server when possible to patch the security vulnerability. The temporary fix just requires adding a key to the registry on the client machine:
- Open the Registry Editor by pressing Start and typing regedit
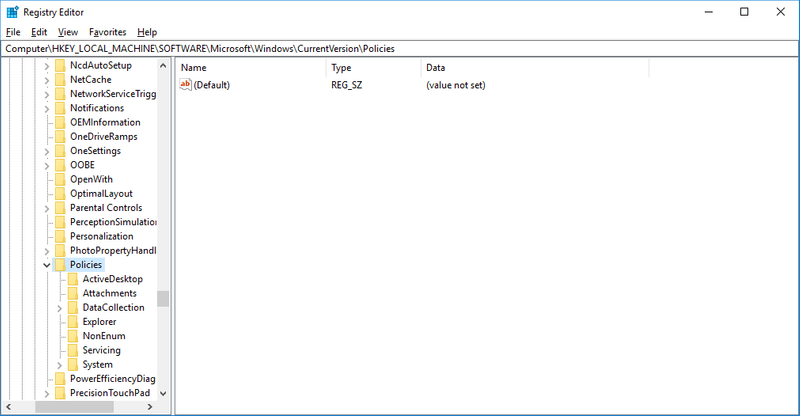
- Navigate to HKEYLOCALMACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies in the left panel:
- Right-click on the System folder and go to New -> Key and rename the key to CredSSP
- Right-click on the CredSSP folder and go to New -> Key and rename the key to Parameters
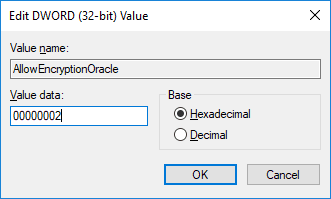
- Right click on the Parameters folder and go to New -> DWORD (32-bit) Value and rename the value to AllowEncryptionOracle.
- Double click on the new value and set the Value Data field to 00000002 as seen below. Click OK
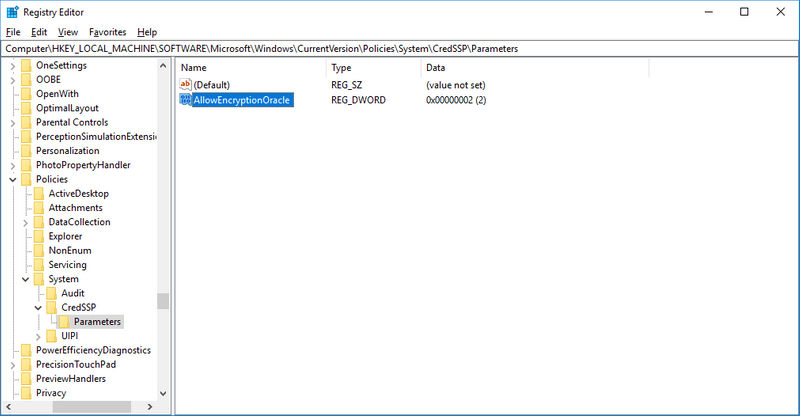
Your registry should now look as follows:
- Restart your computer for the change to take effect
Final Thoughts
That should be all that’s needed to get around the error. Keep in mind that this is a temporary fix though and you should try to update all your servers at the soonest convenient time. If you have any questions or comments, please leave them for me down below.